Smarter Cybersecurity with MVISION EDR
By Dave Howard
Manager, Cyber Threat Intelligence
Among the most persistent challenges facing cybersecurity analysts is the sheer volume of alerts generated within a security operations center (SOC). False positives drain critical resources, distract key personnel, and drive fatigue across cybersecurity teams.
Tools like endpoint detection and response (EDR) can dramatically cut down background noise, enabling analysts to quickly make initial determinations and respond to potential cybersecurity threats. For our customers using McAfee cybersecurity solutions, ECS leverages MVISION EDR to detect, investigate, and respond to suspicious activity targeting endpoint systems. MVISION EDR automatically aggregates critical data from the host and presents that information for security analysts to ingest. We use McAfee as a key component of our endpoint security solution for the U.S. Army—protecting up to 1.4 million endpoints as a part of the Army Endpoint Security Solution (AESS)—as well as on several critical projects for large enterprises across the federal civilian, defense, and commercial marketplaces.
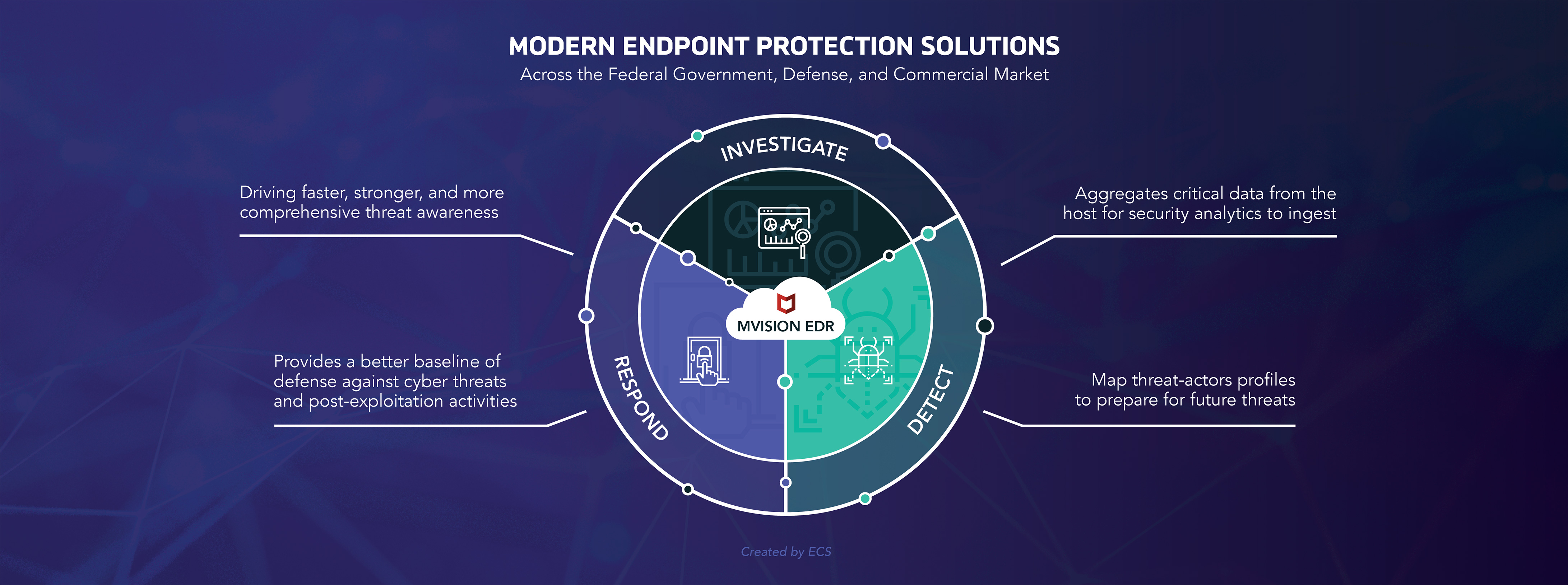
Early endpoint solutions took a signature-based approach, which could only detect known threats. MVISION rolls up the heuristic, artificial intelligence (AI) and machine learning (ML) based approaches of more advanced EDR tools into one package, providing a better baseline of defense against cyber threats and post-exploitation activities. MVISION provides information such as MITRE ATT&CK mapping and threat actor profiles, which helps us understand how an organization was targeted, pinpoint other potential areas of attack, and better prepare for future threats.
MVISION has strong integration capabilities with third-party providers via the Security Innovation Alliance. EDR solutions require two key integrations: security orchestration, automation, and response (SOAR) tools and threat intelligence platforms. MVISION supports this seamlessly. Our cybersecurity analysts curate and constantly update the most timely, relevant, and actionable threat indicators within these platforms, strengthening our back-end data lake analytic capabilities while enhancing our ability to proactively secure an organization’s environment.
80,000,000
Threat indicators augmented
into our platform
But tools are only as useful as the experts who wield them. ECS’ cybersecurity analysts work with our Advanced Research Center (ARC) to monitor the digital landscape, track potential malicious activity, and uncover the latest threat actor tactics, techniques, and procedures. By bolstering MVISION’s capabilities with ECS’ extensive knowledge base and experience, we drive faster, stronger, and more comprehensive threat awareness. Particularly when it comes to the low and slow activity of more sophisticated adversaries, this synergistic approach is critical for detecting, analyzing, and quickly responding to cybersecurity events.







