By David Yang, Team Lead
Endpoint Engineering
Dynamic app containment (DAC) in endpoint security can be complicated without the right systems and tools. ECS has found McAfee’s Adaptive Threat Prevention (ATP) offers unparalleled DAC capabilities, preventing myriad cybersecurity disasters. For it to be effective, though, users must be dedicated to monitoring, aligning and tuning ATP, along with Real Protect and DAC, all of which require time, effort and skill. Let’s take a look at some terms, tools, and tips.
What is ATP?
ATP is the tool that contains both Real Protect and DAC. It is a module that gets installed on the endpoint. ATP has the ability to block or allow files based on reputation on its own. Then, if the reputation is unknown, ATP uses Real Protect or DAC.
The security policy for both Real Protect and DAC are included in ATP.
Real Protect in endpoint security: on-premise and in the cloud
A two-part cybersecurity tool, the Real Protect scanner inspects suspicious files and activities on client systems to detect malicious patterns using machine-learning. The scanner can then use this information to detect zero-day malware.
This innovative tool is one of the only of its kind that uses machine learning for endpoint security, making it a go-to for ECS cyber techs and analysts
Real Protect is client-based as well as cloud-based. Both include dynamic link library (DLL) scanning to keep trusted processes from loading untrusted portable executable (PE) and DLL files.
By seeking patterns, Real Protect can recognize known malware, scanning files and apps to see if they look the same as the malware. While Real Protect won’t recognize a particular file, it will recognize attributes of malware.
Client-based Real Protect
Client-based Real Protect uses machine learning on the client system to determine whether the file matches known malware. If the client system is connected to the internet, Real Protect sends telemetry information to the cloud, but it doesn’t use the cloud for analysis.
The client-based scanning sensitivity levels, which are rooted in mathematical formulas, assign “tolerance” to suspicious activity to assess whether the file matches malware. The higher the sensitivity level, the more malware matches will be found. Allowing more detections can result in more false positives.
Cloud-based Real Protect
Cloud-based Real Protect collects and sends file attributes and behavioral information to the machine-learning system in the cloud for malware analysis. This version of Real Protect also uses machine learning to analyze files to see if any malware-like criteria. Files that come up with a match are blocked.
To run efficiently and stay current, both cloud-based and client-based Real Protect need to be updated, just like any other system or tool. In order to accomplish this, the client software connects to a local or remote McAfee server or directly to a site on the internet. Endpoint security then checks for:
Updates to the content files that detect threats
Content files that contain definitions for threats, such as viruses and spyware
Upgrades to software components, such as patches and hotfixes
Dynamic App Containment: the sandbox and beyond
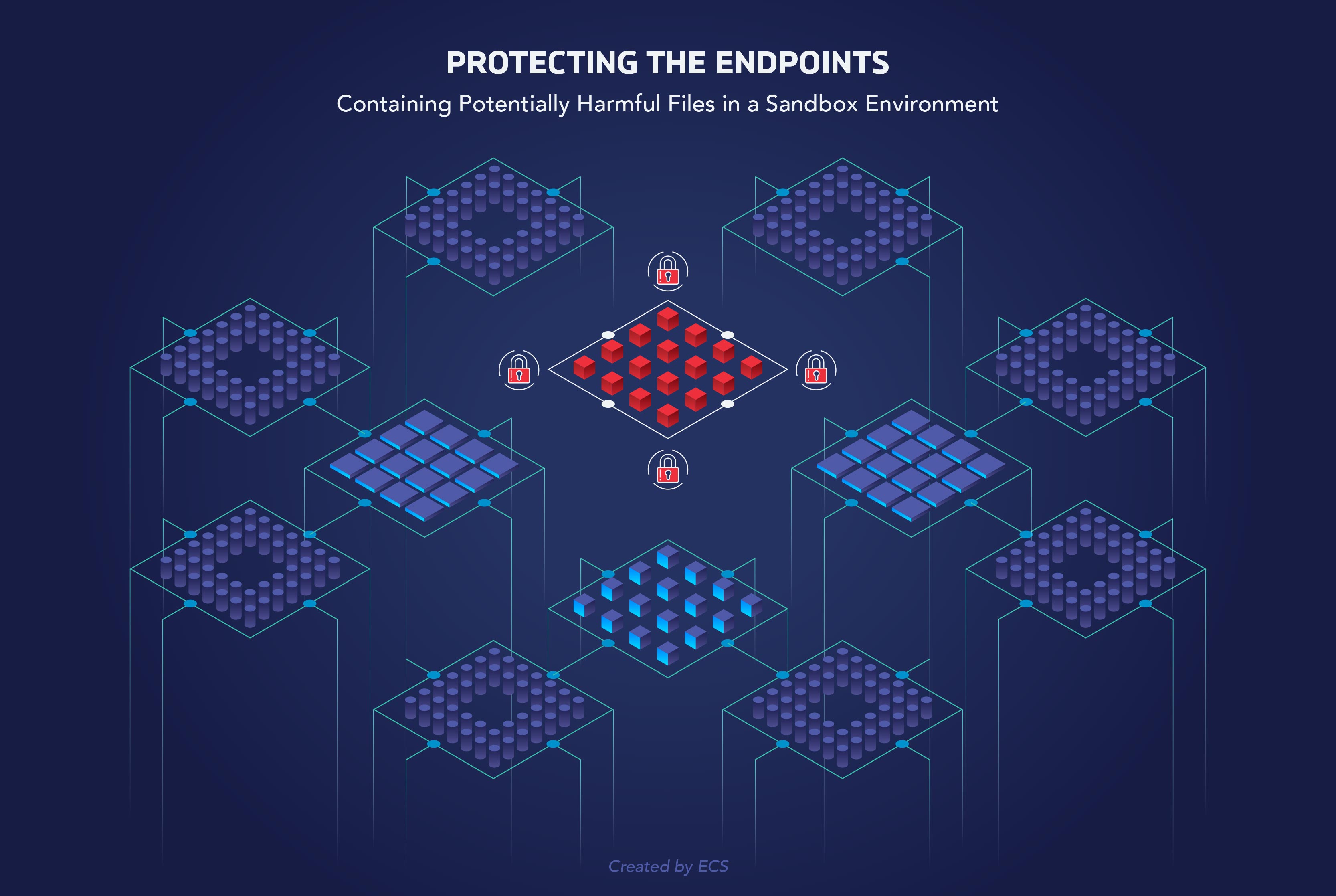
DAC is endpoint protection in a private sandbox. DAC allows unknown files to run in a container (the “sandbox”), limiting what they can do. When a file is sandboxed, it is separated from other programs so if security issues come up, they will not spread to other areas of the network. Based on a file’s reputation, DAC can sandbox a file and run the file against a set of rules. If the file or process triggers enough “block” containment rules to exhibit suspicious behavior, the file is automatically blocked for not following the rules.
Tips for running ATP with Real Protect and DAC
While ATP is a powerful cybersecurity tool, it is not used in a vacuum. ECS takes an integrated approach, combining analytics, threat intelligence, and cybersecurity experts. Therefore, when you decide to use ATP along with Real Protect and DAC, consider integration with other tools from McAfee like Advanced Threat Defense (ATD), Data Exchange Layer (DXL), and Threat Intelligence Exchange (TIE).
You will want to make sure you are running TIE and Global Threat Intelligence (GTI) to collect reputations before enabling DAC. These makes the task of tuning less labor intensive because it aids in automated reputation analysis.
Then, get ready for a lot of tuning, because DAC requires it constantly to sift out false positives.
To help you tune, you will need to build reports around events and based on those reports, adjust tolerance as necessary. Then, address the threats to see if they are actual threats or false positives.
It’s also important to know your environment. If Real Protect is operating in a high-change environment with a lot of developers, set sensitivity to scanning as appropriate, since developers write programs that sometimes have attributes of malware but aren’t, resulting in a false positive.
Give yourself time. Real Protect and DAC’s policies aren’t overly complicated, but it’s time consuming to prepare them to run in a specific environment.
Finally, when you are ready to implement ATD along with Real Protect and DAC, make sure you use the observe node first to avoid blocking too many false positives. You want to ensure the protection is solid but has the least amount of impact possible.
Questions about how ECS manages endpoint security for clients? Read about one of our approaches here, and reach out to an ECS cyber expert for more information.






